DUBLIN AIRPORT - RADISSON BLU HOTEL
DAY 1 TRAINING PASS
(NIS2)
DAY 2 TRAINING PASS (DORA)
PASS FOR BOTH DAYS
(NIS2 & DORA)
EVENT OVERVIEW
Message from Paul C Dwyer
President of the ICTTF International Cyber Threat Task Force
EVENT FAQS
How Do I Access the Live Stream
When are the Exams Available?
How Do I Contact the Venue / Hotel?
What is the Agenda?




Welcome to the 2025 EU Cyber Summit, the premier event dedicated to empowering businesses through robust EU legislation and cutting-edge cybersecurity practices. In a landmark year for European regulation, we are combining the NIS2 and DORA directives into one comprehensive, high-value event, offering attendees a unique opportunity to gain insights into both frameworks.
Since 2011, the ICTTF—International Cyber Threat Task Force—has led the way in shaping Europe's cybersecurity landscape, and this year, we’re taking it further by uniting key players across industries, government, and technology to drive collaboration and innovation. Join us as we explore how these critical regulations will not only safeguard but also enhance the digital economy. Be part of the conversation that’s shaping the secure digital future of Europe

DUBLIN AIRPORT - RADISSON BLU HOTEL
DAY 1 TRAINING PASS
(NIS2)
DAY 2 TRAINING PASS (DORA)
PASS FOR BOTH DAYS
(NIS2 & DORA)
Meet the Experts
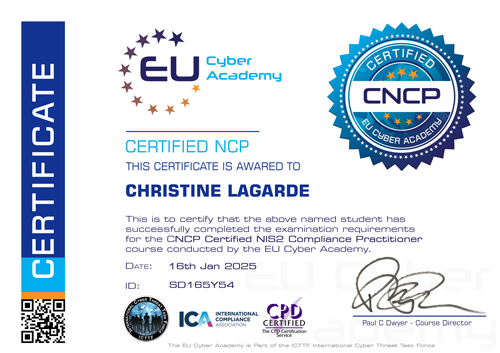
2 DAY Education Programme with Qualifications


Delegates attending the EU Cyber Summit will receive a voucher for each day they attend, allowing them to take an online exam via the EU Cyber Academy.
Day 1 (NIS2 Focus): Voucher for the CNCP exam (Certified NIS2 Compliance Practitioner)
Day 2 (DORA Focus): Voucher for the CDCP exam (Certified DORA Compliance Practitioner)
The International Cyber Threat Task Force (ICTTF) cordially invites you to the pivotal event of the year – the EU Cyber Summit 2025. With over a decade-long legacy of pioneering the most influential and innovative events in cybersecurity, we are charting a new course in cyber education with our most ambitious format yet.
Certified DORA Compliance Practitioner

Certified NIS2 Compliance Practitioner
The Pinnacle of Cyber Education
3 STREAMS
Knowledge Dissemination
The EU Cyber Summit 2025 is structured into three focused streams of content tailored for different audiences:
STRATEGIC STREAM: Aimed at senior decision-makers, this stream addresses high-level strategies for managing cyber risk, compliance, and innovation within the digital economy.
OPERATIONAL STREAM: Geared towards professionals overseeing day-to-day operations, this stream focuses on practical aspects of cybersecurity management and compliance.
TECHNICAL STREAM: Designed for technical staff, this stream delves into detailed aspects of cybersecurity, offering in-depth discussions on technical challenges and solutions.

RECENT EVENT FEEDBACK
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Write your awesome label here.
Workshops
Throughout the EU Cyber Summit 2025, we will host a series of specialist workshops designed to provide in-depth, practical insights into the NIS2 Directive and the DORA Act. These workshops will focus on the key challenges organisations face in meeting compliance requirements, while offering actionable strategies to navigate the evolving cybersecurity landscape. These sessions will provide a unique opportunity for delegates to engage directly with specialists, ensuring they leave with practical knowledge they can apply within their organisations.

A Multifaceted Format
A Call to Excellence
Streamed Live
On Demand for a Month

"IT TAKES A NETWORK TO DEFEAT A NETWORK"
Target Audience
- Cybersecurity Professionals: Those responsible for protecting organizational IT infrastructure from cyber threats, including Security Analysts, Cybersecurity Engineers, and Chief Information Security Officers (CISOs).
- Compliance Officers/Managers: Individuals tasked with ensuring that organizational practices comply with relevant laws, regulations, and policies, particularly in the cyber and data protection domains.
- IT Managers and Directors: Those overseeing IT departments, ensuring the alignment of IT strategies with business objectives, including the integration of cybersecurity measures.
- Risk Managers: Professionals focused on identifying, analysing, and mitigating risks, especially cyber risks, within organizations.
- Data Protection Officers (DPOs): Designated officers responsible for overseeing data protection strategy and compliance with data protection regulations such as the GDPR.
- Legal Professionals Specializing in Cyber Law: Lawyers and legal advisors who specialize in the legal aspects of cybersecurity and data protection, advising organizations on compliance with cybersecurity laws and regulations.
- Chief Compliance Officers: Executives responsible for overseeing and managing regulatory compliance issues within an organization.
- Regulatory Affairs Professionals: Individuals who liaise with regulatory bodies and ensure that organizations comply with all applicable regulations, standards, and laws.
- IT Auditors: Professionals who assess the effectiveness of an organization’s IT systems, ensuring compliance with regulatory standards and identifying potential security weaknesses.
- Chief Executive Officers (CEOs) and Other C-Level Executives: Senior executives interested in understanding the implications of cybersecurity and compliance on corporate strategy, governance, and risk management.
- Business Continuity Planners: Professionals responsible for developing strategies to maintain business functions in the event of cyber threats and incidents.
- Network and Systems Administrators: IT professionals responsible for the daily operation of computer networks, who need to understand cybersecurity risks and compliance requirements
- Human Resources Professionals: Those involved in crafting policies and training programs related to cybersecurity awareness and compliance within the organization.
- Project Managers in IT and Cybersecurity Projects: Individuals overseeing projects related to IT, cybersecurity, and compliance, ensuring projects adhere to regulatory requirements.
- Educators and Academic Researchers: Those involved in the study or teaching of cybersecurity, cyber law, and compliance, looking to update their knowledge and incorporate the latest trends and regulations into their curricula.
- Cybersecurity Innovators, Entrepreneurs, and Solution Providers: Visionary leaders and creators in the cybersecurity space who aim to deepen their understanding of compliance challenges. They seek to identify opportunities for innovation, developing cutting-edge solutions and services that address the complex compliance needs of their clients, gaining insights into emerging trends, regulatory requirements, and the evolving threat landscape.

EU DORA SUMMIT 2024

EU CYBER AWARDS 2022

EU CYBER SUMMIT 2018

EU CYBER SUMMIT 2017
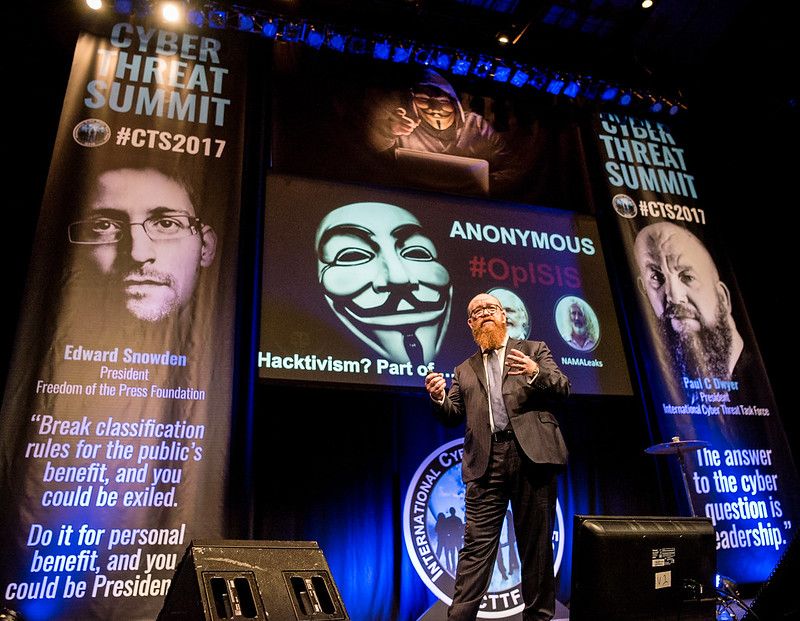
EU CYBER SUMMIT 2017

EU CYBER SUMMIT 2016

CYBER LEADERS LUNCH 2016

CYBER THREAT SUMMIT 2012

CYBER THREAT SUMMIT 2011

THE FIRST SUMMIT - 2011

EU CYBER SUMMIT 2018
Sponsorship Opportunities


Rhonda Reihill
Events Director
P: +353-(0)1-905 3263
M: +353-(0)87 738 8990
E: rhonda@icttf.org

Request Sponsorship Information

HEAD OFFICE
-
ICTTF Ltd
ICTTF House
First Floor Unit 15
N17 Business Park
Tuam, Co Galway
H54 H1K2 -
info@icttf.org
support@icttf.org -
+353 (0)1 905 3263